Document Anonymization Process in an Organization
A well-defined document anonymization process is essential for protecting sensitive information and ensuring compliance with legal regulations. However, many organizations lack a structured approach, leaving employees to handle anonymization without clear guidelines. This increases the risk of errors, unauthorized access, and data breaches. Without proper tracking and control, it becomes challenging to monitor changes, identify security gaps, and maintain compliance. Implementing a standardized anonymization process helps organizations enhance security, improve document management, and mitigate risks associated with handling sensitive data.
Key Elements of an Effective Anonymization Process
An effective anonymization process goes beyond simply removing identifiable information—it must ensure consistency, traceability, and security. A well-structured approach should include maintaining an anonymization history, tracking edits, managing user access, and enabling audit functionalities. These elements help organizations minimize risks, comply with regulations, and maintain full control over sensitive data.
Anonymization History of Documents
An anonymization system should store all relevant information related to document processing. Specifically, it should record the anonymization date, project name, responsible team, number of pages, file type and size, and processing time. This provides organizations with complete insight into the anonymization process and enhances data security control.
Edit Tracking and Anonymization Audit
Every change in a document should be precisely recorded. It is crucial to maintain information on who created the document and when, who anonymized it, and when the original file was deleted. Such transparency allows for better data management and eliminates the risk of unauthorized modifications. The audit functionality enables organizations to analyze operations performed on files, increasing process transparency.
User and Team Management
An anonymization system should allow for assigning appropriate roles to users, such as administrator or standard user, and tracking activities, including user addition dates and recent actions. It should also offer team management features, such as adding and removing users and viewing their roles and email addresses. Access control is essential for ensuring a secure anonymization process.
Document Availability and File Downloads
The system should provide the ability to download files directly from the anonymization history and access the full edit history, allowing organizations to track the entire document transformation process when needed. This enhances document management and security within the organization.
Why Implement an Anonymization System?
A standardized anonymization process not only minimizes the risk of errors but also ensures full control over documentation and regulatory compliance. By establishing clear rules and providing access to detailed data on the anonymization process, organizations can enhance information security, reduce data leakage risks, and build greater trust with clients and business partners. Investing in professional anonymization tools helps prevent potential threats and improves data management efficiency.
Conclusion
Document anonymization is a crucial part of an organization’s data protection strategy. Implementing a structured approach to anonymization allows for full document control, compliance with legal regulations, and enhanced information security. It is worth choosing solutions that enable anonymization history tracking, user and team management, and secure document accessibility in a transparent manner.
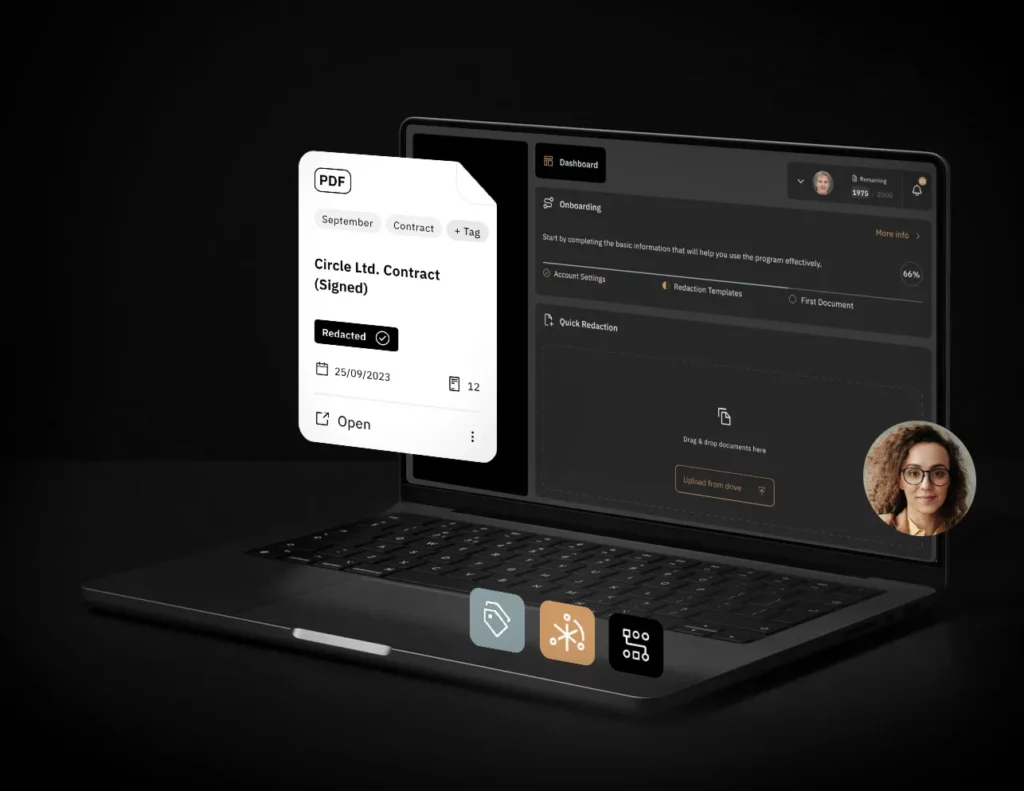
These advanced functionalities are integrated into Bluur.ai, our cutting-edge anonymization solution. A limited number of free trial versions are available—try Bluur.ai today at Bluur.ai!